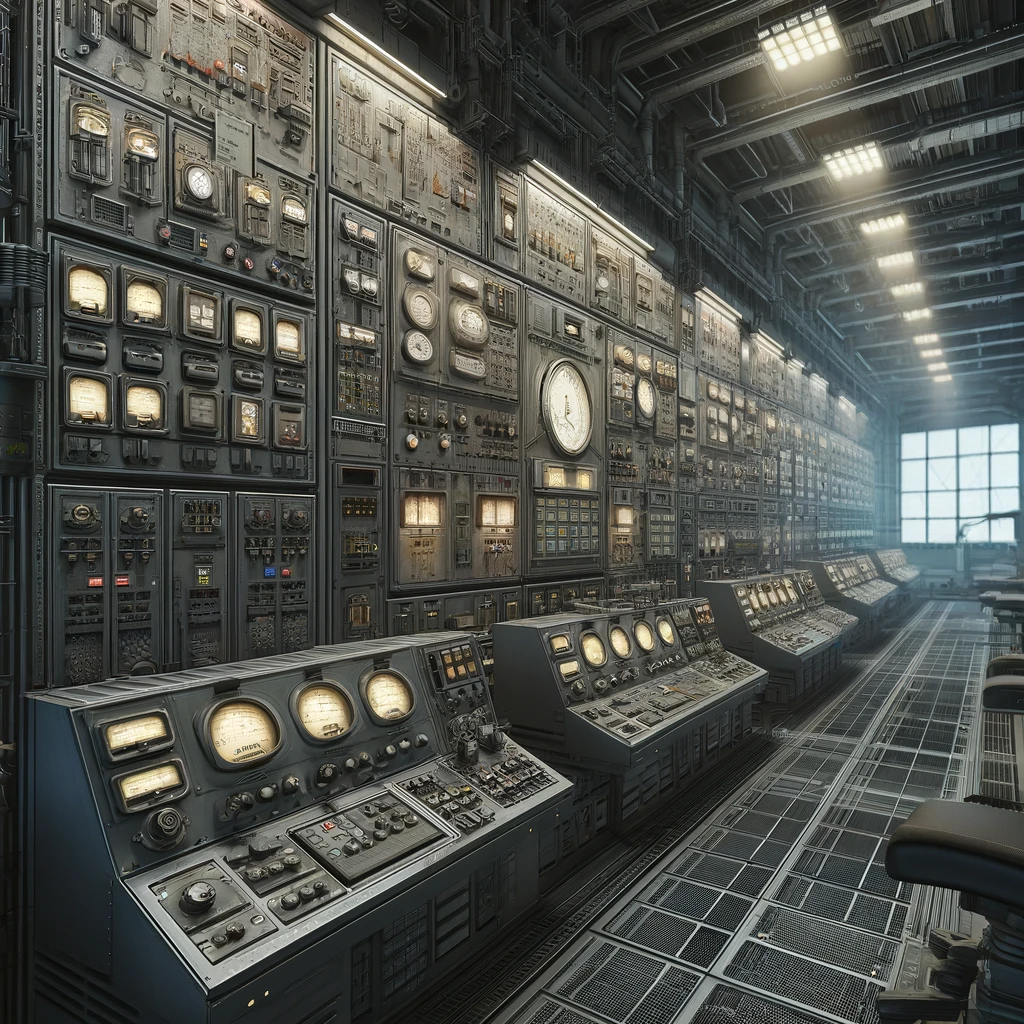
In the wake of the cyberattack that had plunged the power plant into chaos, you found yourself standing alone in the midst of the control room. The room was filled with the silent hum of disabled systems and the soft flicker of emergency lighting casting long shadows across the walls. The task ahead was daunting: to restore the HMIs that were crucial for monitoring and controlling the plant's operations. These systems were your eyes and ears within the facility, and without them, you were blind.
You notice some of the HMI’s have an agent-based backup utility on them. Some of the other screens, usually aglow with data streams and operational metrics, were ominously blank. As you look at some of the consoles in the server room, a familiar interface provided a small comfort in the sea of uncertainty. The software was capable, but the task was complex, involving careful restoration of system backups without reintroducing any vulnerabilities that might have been exploited during the attack.
As you think about this process, you recall a conversation you had at the last Cyber Mutual Assistance in-person meeting where you met another member that also used this same utility. Ironically you both joked about how you hoped you’d never have to use it, and what that experience might be like. You’re really glad your company decided to sign the NDA to become part of the program. Realizing the magnitude of the challenge, you decided to call your new CMA buddy. As the phone rang, you glanced nervously at the inert screens around you.
"Hey, it’s me," you started, once the call connected. "I’m trying to restore some HMIs, but I could use a bit of guidance here."
Your friend’s voice, calm and reassuring, came through the line, "Alright, walk me through what you see. Let's get those systems back online."
Following your friend’s instructions, you navigated through the advanced settings. "Make sure you’re applying the latest secure backup. Check the timestamps," your friend advised, his voice a steady presence in your ear.
As you selected the correct backup files, meticulously avoiding any that were dated close to the time of the attack, your friend continued to provide essential insights. "You’ll need to use the restoration boot media because of the state they’re in."
As each HMI began to flicker back to life, one by one, as the restoration process took hold. "Okay, they’re starting up," you reported, relief beginning to seep through the tension. "I see the boot screens, and... yes, the interfaces are loading up!"
"That’s great," came the response, tinged with satisfaction. "Now, let's go through the configurations to check for signs of the compromise."
With your friend’s expert guidance over the phone, you managed to restore all the HMIs securely. Each screen lit up, bringing the control room back from the brink of operational darkness. As you ended the call with a heartfelt thanks, you looked around at the humming machinery—your efforts guided by a distant friend had turned the tide.
As the adrenaline faded, you were left in the soft hum of the restored control room. The crisis had demanded resilience and a willingness to reach out for help when it mattered most. The HMIs, now fully operational and secure, displayed streams of data that spoke of a plant slowly coming back to life—a testament to your determination and the unspoken bond between those who stand guard over our most critical systems.
You know you’re not out of the woods yet, but the sense of accomplishment is formidable.
Question 8: How many utilities are in CMA?
[accordions]
[accordion title="Clue%201"]
There’s a session for this!
[/accordion]
[accordion title="Clue%202"]
If you’re not a CMA member, who would you ask?
[/accordion]
[accordion title="Clue%203"]
Ask a CS-MAG or NRECA Cybersecurity team member for info on CMA.[/accordion]
[/accordions]
[row]
[column 3]
[button-coop title="Previous%20Section" link="%2Fconferences-education%2Fmeetings%2FCo-op-Cyber-Tech%2FPages%2FComputer-Terminal-inside-Server-Room.aspx" /]
[/column]
[column 3]
[button-coop title="Next%20Section" link="%2Fconferences-education%2Fmeetings%2FCo-op-Cyber-Tech%2FPages%2F9-Server-Room.aspx" /]
[/column]
[column 3][/column]
[column 3][/column]
[/row]
CTF sponsored by:
[row center middle]
[column 4]

[/column]
[column 4]

[/column]
[column 4]

[/column]
[/row]
[row center middle]
[column 4]

[/column]
[column 4]

[/column]
[/row]
